

TURN is a great show. Very compelling, some truth to it although not the main characters or the spy ring itself. Finishingsn episode always leaves me wanting to immediately watch the next.
Obligatory, fuck Simcoe.
Bit-breaker working in cybersecurity/IT. Only languages I know are English and Programming ones.
Sometimes I write things about technology.
If I told you the SHA256 for this sentence starts with 'c, 5, four, a, and a', would you believe me?


TURN is a great show. Very compelling, some truth to it although not the main characters or the spy ring itself. Finishingsn episode always leaves me wanting to immediately watch the next.
Obligatory, fuck Simcoe.

Not why it’s there or supposed to be used for…


Some key components of Sailfish OS have been licensed proprietary by Jolla from the start and ever since (as of Sailfish OS 5.0 in February 2025). Since September 2025 some closed parts of Sailfish OS have been open sourced, with the announcement that more parts are to be followed.
The oldest shark teeth are from the Early Devonian, about 410 million years old. These are without a doubt sharks, although different species than exist currently. The earliest fossil of a plant engaging in this evolutionary strategy is a 12 meter tall palm-like plant from China. It dates back, again, to the Early Devonian, but less than 400 million years ago.
Which means the first toothed sharks predate the first plant which could be called a tree by 10 million years.
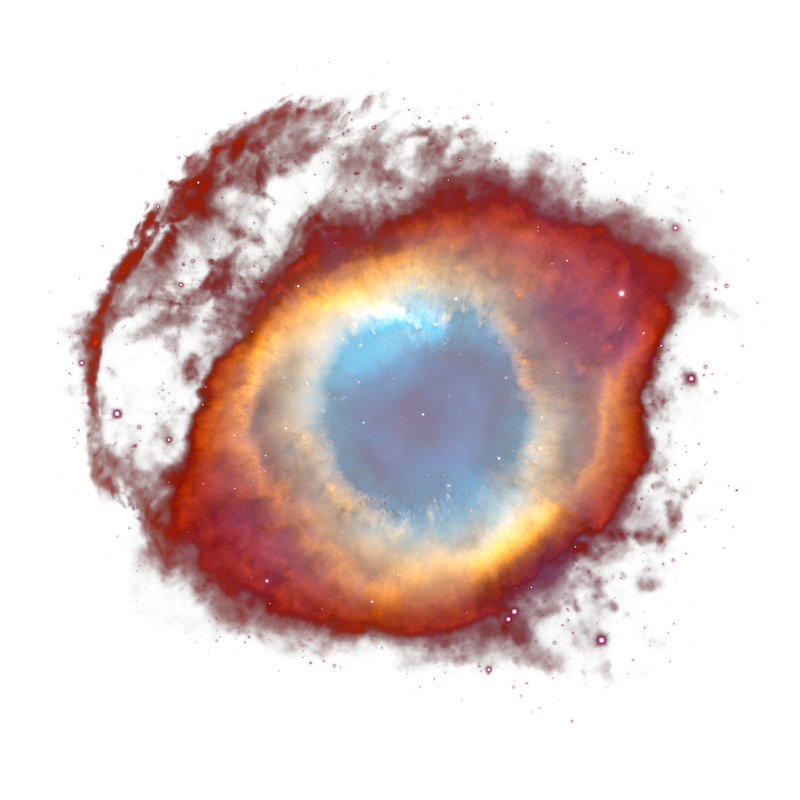
Sharks are older than the rings of Saturn!


I cannot believe that was actually said by a United States representative, where it is and has been codified in the nations constitution, that freedom of religion is a right of the people via the first amendment. Freedom of religion means any religion, but also, freedom from religion.
to wit: The civil rights of none shall be abridged on account of religious belief or worship, nor shall any national religion be established, nor shall the full and equal rights of conscience be in any manner, or on any pretext, infringed.


For 70% of the companies out there, If your company or website collects it; hackers will get it. Your PR ‘trust us’ words have no meaning or substance.


People don’t generally quit bad jobs, they stick it out for whatever reason. They do quit having a bad boss though.


There’s a really nice high level overview of TOP/MFA by OWASP
They say:
There is no definitive “best way” to do this, and what is appropriate will vary hugely based on the security of the application, and also the level of control over the users. Solutions that work for a corporate application where all the staff know each other are unlikely to be feasible for a publicly available application with thousands of users all over the world. Every recovery method has its own advantages and disadvantages, and these need to be evaluated in the context of the application.
Some suggestions of possible methods include:
- Providing the user with a number of single-use recovery codes when they first setup MFA.
- Requiring the user to setup multiple types of MFA (such as a digital certificate, OTP core and phone number for SMS), so that they are unlikely to lose access to all of them at once.
- Mailing a one-use recovery code (or new hardware token) to the user’s registered address.
- Requiring the user contact the support team and having a rigorous process in place to verify their identity.
- Requiring another trusted user to vouch for them.
The most important thing I think is, the MFA reset should have a different method and flow than the password reset option. Figure if an attacker attempts the ‘forgot password’ method, it’s assumed they have access to the users email. Therefore, you don’t want to send a ‘reset MFA’ in the same manner. The password recovery flow should be separate to the MFA recovery flow by using some form of out-of-band verification such as sending a password reset link within a “forgotten password email” containing a randomly generated and unique token that allows the user to reset the password only. The MFA recovery flow should work in a different manner. If you are offering TOTP only, I suggest offering a fallback method in place such as a list of “backup codes” of valid OTPs that the user needs to keep safe, and is obtained when first enrolling in MFA, or otherwise an OTP sent via SMS with a short expiration time. Ask for the TOTP while entering a new password. The reset link would be useless for the attacker.


Unnecessary. It’s a damn text editor. Leave it simple.

Add it to the list of illegal shit his administration has been doing.


A computer (AI) can never be held accountable. Therefore, a computer (AI) must never make any human decision.


And yet the prices for consumers will not reflect such. MOAR PROFITS! YAY.

“I wanted to be a good boy,” Trump said, describing his relative restraint
AAHahahahaaaaaaaaaahhaaaaaaaaaaaaa. Oh, what a POS.


The linked article has improper HTML for the link to the source. https://news.samsung.com/global/samsung-electronics-and-kt-corporation-verify-x-mimo-technology-in-7-ghz-band-for-6g-development
Is what it points to.

What error messages are yo getting?
Back in the day I used tintin and even got a stripped down copy working on android. That experience I don’t recommend.

Praise be to Odin.

Fun? Lua, Odin, nim, zig.
Impractical? Brain fuck.


Definitely need to learn the key concepts and processes first. But give nfpm a try.
Well no shit. Basic survival is taking a good 80% of the paycheck. Probably CC and other debt takes the remaining. Maybe a few bucks left for a fancy coffee or red bull. Ain’t got no time or money for Healthcare or vacations.