- 25 Posts
- 192 Comments

 82·vor 1 Jahr
82·vor 1 JahrCertainly valid that there isn’t a cultural norm for it in the US. With that said, the US still has about 3.3 million EVs on the road. Norway has about 3.4 million cars on the road total.
So it’s a heck of a lot easier to enable 5.5 million people to replace their cars then 330 million people. Size matters as much as the identity we have with it on this one.

 5·vor 1 Jahr
5·vor 1 JahrAs I’m here now, I can attest to the great public transit. However I will also say the large and dispirit nature of their population means the car will still likely rule. Yes many may not afford it, and some prefer the bike (even now in winter) but they seem to love their cars as much as the US given the traffic.

 181·vor 1 Jahr
181·vor 1 JahrI’m not saying they aren’t downplaying it, but it’s also a population of 5.5 million of highly educated and high per capita income, which makes easier to implement. Small population and people who can afford it.
Not precise in my language, but I meant the same thing. It’s a 180 from current policy vs what Trump will do, but I was hoping it would be more tempered and less shocking. Still shocking, still absurd.
 1·vor 1 Jahr
1·vor 1 JahrIt’s a very different context if read as if you are on a ship.
Makes me wonder if you won’t see and Andrew Carnegie of this era step up and endow it against his fellow capitalist.

 13·vor 1 Jahr
13·vor 1 JahrCurrently ongoing until Jan 5 2024. $10 per ticket. https://shop.proton.me/products/2024-lifetime-raffle-ticket
Where will the funds go?
Proceeds will go to 10 organizations selected with the support of our community and to a handful of past fundraisers beneficiaries, with Proton matching up to $150,000 in donations. The new recipients this year are:
- Freedom House
- Free Software Foundation Europe
- OpenStreetMap
- The Tech Oversight Project
- Ladybird Browser
- Nothing2hide
- Open Data Institute
- Ada Lovelace Institute
- Law for Change
- Free Press Unlimited

 15·vor 1 Jahr
15·vor 1 JahrThis is fascinating as I didn’t even know about it for one, and for two it’s based on having legal standing as a customer of the product, not the developer of the GPL code. I’ll be interested to see where this goes.
Tracking can and is done with both by 3rd parties.
Not the best link, but Schiphol airport as a public example.

 5·vor 1 Jahr
5·vor 1 JahrGood thing they found some in Montana. Not that it’ll be online for a while.
I think the market is going to struggle with this for a while yet, in the mist of this brewing trade war.

 33·vor 1 Jahr
33·vor 1 JahrGIvesendgo legal fund for those who want to see.
 41·vor 1 Jahr
41·vor 1 JahrAs Ryan Broderick put it in his Garbage Day newsletter on Monday, “It’s possible that this is the most aligned America—well, aside from the folks in its highest tax brackets—has been about a news story since the invention of the internet.”
Want further proof? Look no further than the comments on Daily Wire host Ben Shapiro’s YouTube channel. On a video titled “The EVIL Revolutionary Left Cheers Murder!” the responses were swift and unequivocal: “FACT: Both left AND right are cheering! We don’t care about your feelings”; “I’m not buying this ‘left vs right’ shit anymore Ben, I want health care for my family”; “Just because ‘the left’ likes something doesn’t mean you have to instinctively hate it. Wake up and read the room bro.” Not exactly the kind of banter typically found in the comments section of a manosphere video.

 2·vor 1 Jahr
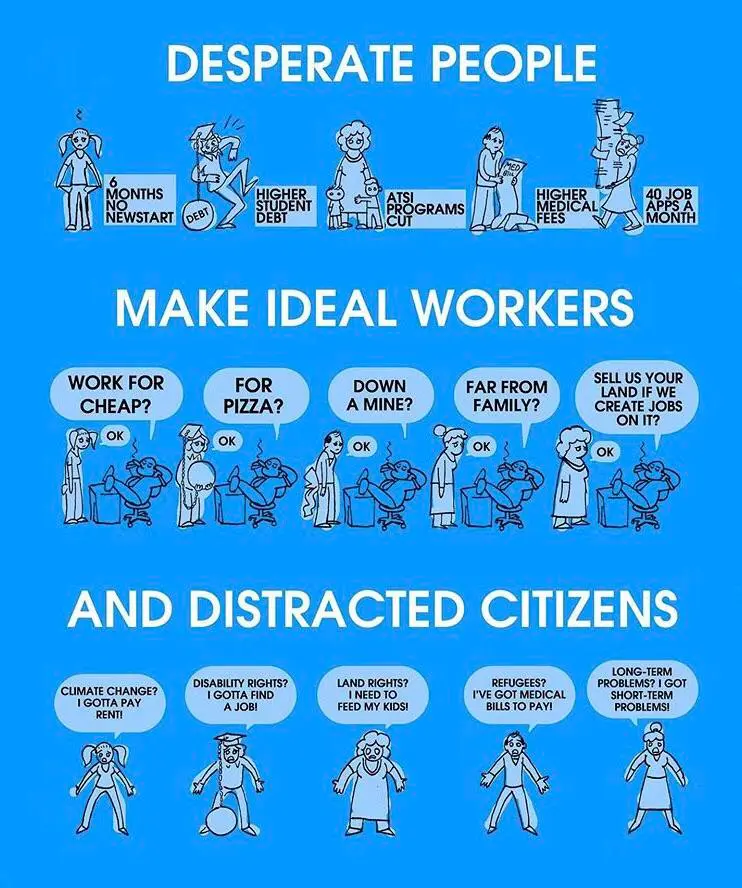
2·vor 1 JahrThey had their chance at the voting booth… Fighting the good fight is hard when people vote against their interest.

 8·vor 1 Jahr
8·vor 1 JahrNot all care, but it still impacts them.
Beyond this, the diurnal cycle does filter down into the disphotic zone and does influence species. It does weaken with depth.
 1·vor 1 Jahr
1·vor 1 JahrBut the current rule also allows companies to leave out key details. For example, Exxon, Chevron and other firms including Transneft, a Russian state-owned company, are partners in the Caspian Pipeline Consortium. CPC pays hundreds of millions of dollars in taxes and fines to Russian governmental authorities. These taxes help sustain the Russian economy, boost arms production and pay state officials’ salaries and pensions — thereby aiding the Russian war effort in Ukraine.

 16·vor 1 Jahr
16·vor 1 JahrAddiction is a tough thing… Hard just to out it down.

 2·vor 1 Jahr
2·vor 1 JahrLook, yes avoidance is a valid behavior. We have it, we need it, and it’s useful at times, but like any behavior it can become a dependence. Wholly depending on an attitude of avoidance to deal with the outside world doesn’t build resilience. Desensitizing to the trauma and being able to face it, and act in spite of seems like a better goal.
It’s a screwed up depressing world and I empathize with the horror, disgust, disillusionment, disenfranchised nature of the world.
I struggle with it constantly, and maybe we should create a support group or a sub for this alone, as we need to find ways to cope with this, as it’s not going to get fixed in a vacuum. Yet we can’t fix it if we are overwhelmed and emotionally shutdown…




















And this is the nuanced answer that begins to give context to the issue.
Absolutely correct.