The Linux kernel is less secure for running untrusted software than a VM because most hypervisors have a far smaller attack surface.
how many serious organization destroying vulnerabilities have there been? It is pretty solid.
The CVEs differ? The reasons that most organizations don’t get destroyed is that they don’t run untrusted software on the same kernels that process their sensitive information.
whatever proprietary software thing you think is best
This is a ridiculous attack. I never suggested anything about proprietary software. Linux’s KVM is pretty great.











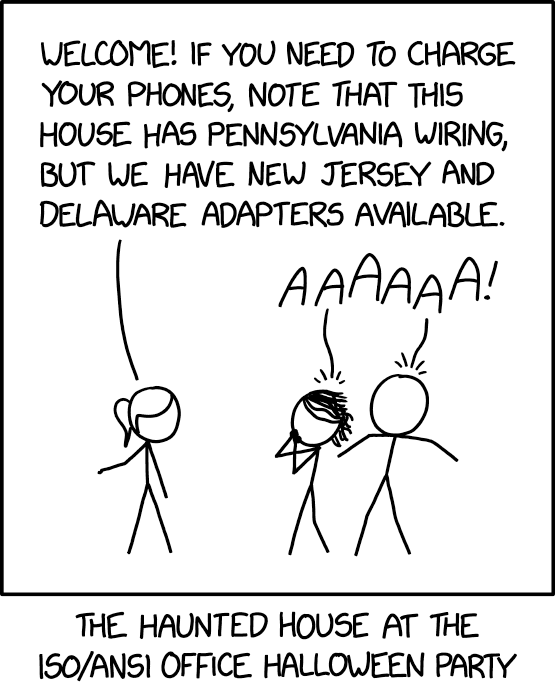








To be fair this doesn’t sound much different than your average human using the internet.