… to combat online child exploitative material, fentanyl trafficking, romance fraud, money laundering…
How is romance fraud at the same level as child exploit or money laundering? These assholes want to take full control of the world population.
They just wanted to pack that list. Who thinks child exploitation is a true concern while nothing is done about the Epstein file?
This is all very bad. But, much like with the tools used during the War on Terror to track “potential terrorists”, I suspect this system has a problem of excessive false positives and false correlations.
Historically, the response to this kind of data sweep was not to target people based on the information but to justify targeting of people after the fact. Also, the FBI made a habit of setting out honeypots for (typically mentally ill or extremely naive) would-be radicals or even radicalization programs intended to foment prosecutable misconduct where none had existed.
Case in point, the Newburgh Four
In 2008, FBI-paid informant Shahed Hussain met James Cromitie in the parking lot of a mosque in Newburgh, New York, a town with a high poverty rate and large Muslim community. (Cromitie was not part of the compassionate release request that has set the other three free.) Hussain befriended Cromitie, a down and out petty drug dealer. Hussain claims to have told Cromitie that he was a member of a terrorist organization in Pakistan, which Cromitie allegedly expressed interest in joining. In subsequent recorded conversations, Cromitie made hateful antisemitic remarks, but according to evidence presented during the trial in 2011, when Hussain encouraged him to “make a plan, pick a target, find recruits, . . . procure guns, and conduct surveillance,” Cromitie did nothing. Hussain sought to motivate Cromitie by assuring him he would be rewarded in the afterlife for a jihadist attack, to no avail.
Hussain began offering more significant financial incentives for executing an attack, including promising Cromitie a BMW and cash, but Cromitie remained uninspired, taking no action to develop an attack plan. Even FBI agents thought that Cromitie was “unlikely to commit an act without the support of the FBI source.” Hussain’s enticements became more extravagant, including offering to pay Cromitie $250,000, an unauthorized inducement the FBI captured on a wiretap. Apparently tempted by the big payoff, Cromitie accompanied Hussian to scope out a potential target, but thereafter avoided Hussain and his persistent attempts to resume contact.
Cromitie avoided Hussain for almost two months. After losing his job and desperate for money, he reinitiated contact with Hussain and agreed to plot an attack. At Hussain’s urging, Cromitie recruited other Muslim men, David Williams, Onta Williams (no relation), and Laguerre Payen, to serve as lookouts. Like Cromitie, they too were impoverished with histories of petty drug crimes and mental illness. With the four men along for the ride, the informant Hussain pushed the scheme forward, selecting a synagogue and U.S. Air Force base as targets and driving the defendants across state lines (to ensure federal jurisdiction) to pick up mock weapons arranged by the FBI.
If these programs are allowed to run their course, I suspect we’ll see similar stories springing up as less ideologically motivated judges recoil at investigations and prosecutions where the crimes themselves are entirely orchestrated by the investigating agencies.
It really occurs to me that this emphasis on surveillance (Palantir, this Discord stuff, the cameras everywhere, etc.) really shows how afraid the billionaire class is. They’re trying to identify those that are getting uppity to try and prevent organizing, which they hope would quash revolution. They know people are angry; they know they’ve been looting and pillaging; they know they’ve been denying access to badic things like food, housing, healthcare; and they know they work for hostile interests. Yet, they’re going to keep on doing it. They even have a new police force.
It never works though.

It never works though.
If you get under the hood of Mangione’s actual history and ideology, the guy was an Effective Altruist insider. Not some Far-Left Antifa Radical, but a staunch techbro anarcho-libertarian who initially sympathized with Balaji Srinivasan’s Network State and Peter Thiel’s vision of fully capitalist Start Up Cities.
He’d never have normally registered on a dragnet like this.
But, more importantly, he’s a near-singular instance of vigilante violence against a business executive. To say “it never works”, you need to ignore the enormous security apparatus surrounding Fortune 100 senior executives. And the relative infrequency of these attempts in general. Since Thompson, there hasn’t been some wave of executive assassinations. The closest we’ve seen was another lone wolf shooting of Charlie Kirk. Has a billionaire ever been deliberately targeted and killed… ever?
Whether it is through a reasonably robust security state, a militantly apathetic public, or the general anonymity of business executives, the real physical risk to billionaires and their CEO stogies appears to be nearly zero.
I opened Microsoft Solitaire on my phone the other day and the fucking thing wanted to age verify me. Over on the desktop the same thing happened in MS App Store. The stupid part? I’ve had this Microsoft account for so long that it legally qualifies as an adult in its own right.
We should all just take pics of our taint and send that in. Malicious compliance.
They’ll just forward the data to the butthole database; we still lose ✨
Playing the entire Bee movie to reporting hotlines for ICE worked for a bit. Let’s kick it up a notch.
Off to take some photos of bee taints, I guess
I thought discord moved to k-id and ditched this system?
It did, the dateline in this article is from February 19th.
Why can’t people just go down to their local shop, show their ID like when you buy alcohol, and buy some kind of age verification token/code which can be used with online services?
Cause the goal has never been to prevent underage access it’s to create a database of troublemakers and brown people
my id has an nfc chip built in, I can scan it with my phone to confirm my identity. if only online services could implement an identity check that way.
if only online services could implement an identity check that way.
Outside of banking and taxes, I can’t think of a single online service that I want verifying my identity. Ostensibly, these services just want to verify if you’re of legal age. The small, binary question of “Are you over 18?” should require much less private data than would be needed to verify my identity.
My point wasn’t one of convenience, but more one of privacy. What’s the difference between someone demanding a photo of your ID (and then storing it) and someone taking the same information from an NFC scan and then storing it?
I don’t know about other countries, but the german e-ID for example is more sophisticated than that. It can actually limit access to the information that is necessary for the given application (your terminal or app shows you what specific information is requested before you confirm via PIN). So it can just return “yes/no” to the question “is this person an adult?” Almost no company uses it, likely because they can’t steal data that way.
They can! In fact, in the UK some government services do this already however there’s a couple of drawbacks:
-
They’d need to use some kind of companion app for each device since the web APIs won’t give them access to this.
-
For us at least the NFC chip still contains a digital copy of the photo so it’s not really any better since I don’t know what data is going to be sent by the app.
Maybe I’m wrong then, but I just kinda assumed that when I log into some government platform by scanning my ID with an official app all it does is it confirms my identity and sends some kinda encrypted token to the api of whatever platform I’m trying to access.
Although if that’s not the case then yea, I guess that wouldn’t be very anonymous either.
-
because that would be sensible and privacy-friendly, and our governments are controlled by fascist pieces of shit that want to have full control over us.
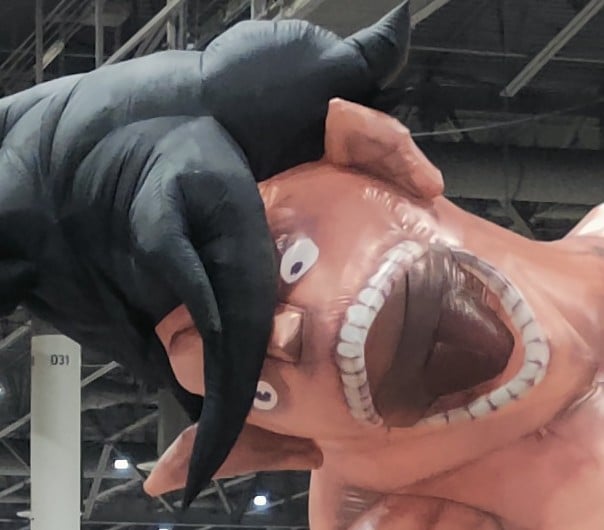
What? But Discord pinky promised that pictures would stay on my system, and be deleted immediately after verification. Are you implying that they lied? Pikachu shock face
This title isn’t what the article says at all. There’s a secondary system completely separate from persona’s main system, that is seemingly tied to openai and government systems, most likely tied to ICE.
If that’s what they said literally (pictures stay local) then they probably didn’t say that the face data leaves the devices
I’d have to double check, but I also don’t think they said the picture would only be used for age verification.
You will only be checked if you want access to adult servers or servers with adult sections, so there’s a decent chance you won’t be affected by the change either way. However, if Discord fails to properly verify you with the information it has, you will have to give your ID and/or a face scan “through trusted partners.”
Discord says it only receives the age of users, and identity details given in the verification process are not associated with your account.
Perhaps partners will receive account info but Discord won’t receive identity? If Discord collects and shares a lot of data then maybe they can correlate account metadata with identity
“This person looks like they might commit a crime in the future. You guys should go arrest him before that happens so we can ‘zero out crime’ in our neighborhoods.”
The neighborhoods where crime has been ‘zeroed-out’:
Also plot of Psycho pass… Spoiler it didn’t eliminate crime…
Someone is disagreeing with the Sybil System? Let’s have your criminality coefficient checked.
Literally that one episode of Futurama
Literally the movie Minority Report
Precogs are machines in our version.
Which one?
“Why wouldn’t I use verification? I’ve got nothing to hide”.
This. This is why you do not submit willingly, regardless of what you have to hide. Fascism doesn’t give a shit if you’re innocent.
“I’ve got nothing to hide”.
That’s not for you to decide.
We’ll determine that after several days of brutal torture. If we determine that you’re telling the truth, then you’ll be free to go. No harm, no foul.
Innocence proves nothing.
“Suspicious how defensive you are getting about your innocence towards the crime we’ve accused you of committing.”
Depending on context my favorite answers to 'Why do you need privacy if you have nothing to hide ?" are
“I need privacy, not because my actions are questionable, but because your judgements and intentions are.”,
“Arguing that you don’t care about privacy because you have nothing to hide is no different than saying you don’t care about free speech because you have nothing to say.” - Edward Snowden,
and “The only difference between a wizard hat and a dunce cap is the wide brim of privacy.”
ETA: None of which a fascist will give a shit about, but can be useful in politer society.
My favorite is:
“So take off your pants. Right here, right now.”
Gets the point across quickly and viscerally.
This is good but I prefer demanding they unlock their phone and hand it to me.
What do you do if they drop trou?
Inspect, very carefully, and point out every detail of course
Take a photo, and use that for face ID.
Or call the cops.
Jokes on you, not wearing any (and how would you know on the other side of a cable) ;)
I get your point but I think there are higher levels here than just a nudity taboo.
The point is to counter the dumb “I have nothing to hide” statement. It simply isn’t true. If that evolves into a deeper convo, good.
This exactly. It’s meant to open up the conversation.
Fair cop, not my style, but you do you.
Using Microsoft teams at work, it keeps on asking me record a voice sample and selfy so it can identify me in meeting , yeah no thanks
Woof. Every time I open a Word doc at work, I now get a pop up saying I’ve disabled location services in my system settings. Why the fuck does Microsoft need to know my location for opening a Word doc?!
And then your coworkers think you’re IT challenged because you don’t even know how to do the simplest things. (true story)
My company just mandatorily implemented “Windows Hello”
No one seems to be able to tell me why the information from Microsoft says the fingerprint and face scans are both “local only” and may take 24 hours to sync after initial setup. Where are they syncing to?
(I opted for the ‘pin’ method instead of surrendering my biometrics.)PIN is the best way to go there. It only works on that one machine, although you can technically set the same PIN again on another computer.
I believe the typical intent is as follows:
- It is now possible to brute force things that were previously considered “complex” passwords in a semi-reasonable amount of time.
- This necessitates longer and more complex passwords
- People can’t remember those so they have a tendency to write them down or do other relatively insecure things with them.
- Forgotten passwords can generate a lot of helpdesk calls and are also an attack vector
- If we insist on really complex passwords that are too long to reasonably brute force with current technology, we need a way for users to log in that’s not going to make 3 and 4 a major issue.
- If the simpler PIN method is locked to a per machine basis, it matters a lot less if the PIN is compromised because you also need physical access to the computer or the PIN is useless.
This should, in theory, allow workplaces to set requirements for really complex passwords that only need to be reset once a year or so, without breaking helpdesk, inconveniencing users, or leaving gaping security holes.
Whether or not that all happens depends on the workplace, but that’s the general thought process in most of the places I’ve worked where a modicum of sense prevails
…. Oh!
You just explained a question I had.
I couldn’t figure out why a pin was considered more secure.In my reasoning: How is a PIN (potentially numeric only), changed 1x a year, safer than a password (3 of 4: Alpha, Mixed case, numeric, special chars), changed 4x a year.
The answer, as you explained, is scope of trust. Machine only vs tenant-wide. That makes sense.
Windows Hello ties the PIN to the TPM of the computer. It’s not just you having a pin, its the pin + the crypto secret loaded on the device. Thats why its more secure then just a complex password.
That makes sense. Something you have (that specific machine) + something you know (your pin).
I used to work someplace where we all had a pin+a smart card that we’d insert into the machine, same idea except I could log into any machine with the card+pin combination.
Loved not having to remember a long AF password. Didn’t like having to drive home if I forgot my card on the kitchen counter.
My assumption is that they are recorded locally, then hashed, then the hash is sent to Azure (Microsoft cloud) as Windows Hello leverages some cloud features. Some things in Azure have warnings about taking up to 24 hours to take effect.
Hashing locally and sending the hash to a server is the same way all passwords for online services and systems work, so nothing nefarious there.
There’s probably perceptual hashing so they can count 95% similarity as a match without having to check against the source material every time.
I could accept that it has to do with azure propagation delays, but the verbiage was explicit about our computers syncing to the tenant. (Vs. data propagating across it.)
I sort of reject the idea that there’s nothing nefarious going on. The misdirect is weird.
Unless they’re salting the hashed data with information they can’t access, they’re just creating a database of faces and fingerprints.
Sure, maybe if their cryptography is good the DB cannot be reversed but they can still use an unsalted database to give match/no match info on scans of faces and fingerprints submitted to it.
But also, I firmly don’t trust Microsoft. They’ve violated our ELA several times - mostly around applying analytics tools to our data without consulting us first. (Like rolling out MS Viva without telling us.)
Whether there’s “nothing to hide” is an assessment made by the fascists and not by the people giving out information.
“If you have nothing to hide, why are you wearing pants? Why don’t you tell me your password?”
I wear pants to protect my password! No, please! Don’t hit me in the password!

Ooof, right in the password! That’ll leave a mark.
And then a new president comes into office or just changes their mind and now something that used to be innocent is now a violation. Luckily the government recorded everything you ever said and did, so knows exactly who to arrest.
“We have determined based on the shape of your nose that you are Jewish. Please follow us to the nearest train.”
“We have determined based on the shape of your nose that you are not Jewish. Please follow us to the nearest train.”
Robinhood also uses Persona and may not allow you to transfer money out without providing ID and face scans.
Well, now I see why there was an avoid OpenAI movement. They actually allowed Persona to create an internal database of their users and may be a potential AI provider for gov surveillance.
Since when did OpenAI started using Persona, and is it widely known that they use it ? Does anybody know? I used their service way back at gpt 3.5 days, back then you didn’t need any verification.
It seriously gets worse the more you read and hear about their “verification system”.
What’s next, some kind of psychological profile based on the bumps and grooves of my skull?
What’s next is that they are going to guilt you in to accepting it because it’s “to save kids from pedophiles and if you don’t fork over your ID, you’re either helping pedophiles or you are a pedophile yourself.”
And it’s going to work. You’re going to go along with it.
Reddit implemented this for brits months ago and there has been no mass exodus. They all forked over their IDs to save the kids. They’re probably all stuck on Discord too assuming everyone who’s leaving is a pedophile. Once KOSA and EARN IT pass here in the US, we also will go along with it, to stop the pedophiles.
“Won’t somebody think of the children?”

To verify that you are permitted to use our platform, please answer the following prompt: You’re in a desert walking along in the sand, when all of a sudden you look down and see a tortoise…
What one? What desert?
Do I know the tortoise?
Does it owe me money?
Godamn will y’all stop writing their next steps out for them to create the newest dystopian hellhole update
I see that your profile indicates some reservations about synergizing with the Torment Nexus but have you considered the value it brings to the shareholders?
Must collect .00000001% more dollars per unit, it’s only billions of lives after all
Urge to maximize paperclips rising…